Data Handling Practices for Private Investigators in Sydney
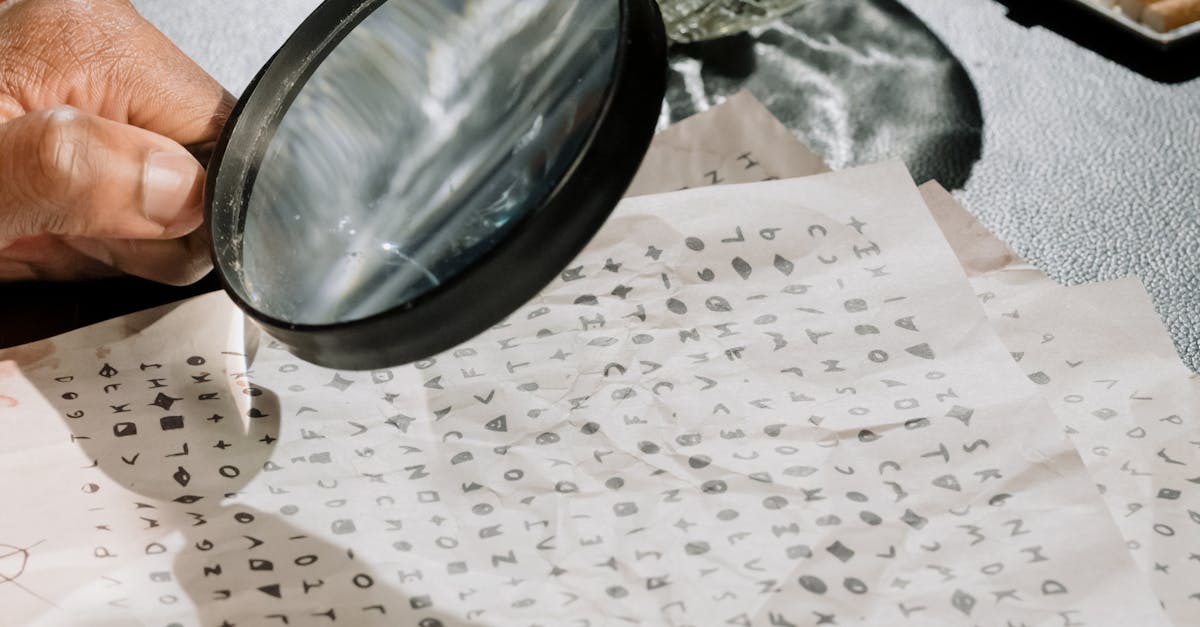
Table Of Contents
Techniques for Data Retrieval
Private investigators in Sydney often utilise multiple techniques for effective data retrieval, essential for their investigative processes. One common approach involves leveraging online databases and public records, which provide valuable information about individuals and businesses. Advanced search techniques, including the use of specific keywords or Boolean searches, enable investigators to filter results more efficiently. In addition, some investigators may employ techniques such as social engineering to gain access to information that is not readily available through conventional methods.
Field investigations play a crucial role in data retrieval. This can involve interviewing witnesses, surveilling locations, or gathering physical evidence. The combination of digital and traditional techniques allows investigators to build comprehensive profiles of subjects, leading to more informed decisions in their inquiries. Investigators must remain adaptable, employing various methods based on the unique circumstances of each case to optimise outcomes.
Tools and Technologies Used by Investigators
Private investigators in Sydney utilise a variety of tools and technologies to enhance their data handling capabilities. Software solutions for data analysis enable them to sift through vast amounts of information quickly. Many investigators incorporate geographic information systems (GIS) to track and visualise data points related to their cases. Surveillance equipment, such as high-resolution cameras and digital recorders, also plays a crucial role in gathering evidence.
Cloud storage solutions have become increasingly popular among investigators, allowing for secure backup and easy access to data from anywhere. Encryption technologies ensure that sensitive information remains protected from unauthorised access. Automated data collection tools streamline the process of gathering necessary information while minimising the risk of human error. These technological advancements facilitate a more efficient investigation process, enabling private investigators to provide accurate results for their clients.
Risk Management in Data Handling
Private investigators must be vigilant when managing sensitive data. Implementing strong security measures is crucial to protect client information. This includes using encryption for stored files and ensuring secure methods for data transmission. Regular audits of data access and handling procedures help identify any vulnerabilities. Establishing protocols for data retention and disposal can further minimise risks associated with sensitive information.
Educating staff on the importance of data security enhances overall risk management efforts. Training programmes should cover the latest trends in data breaches and emerging technologies that could threaten privacy. Investigators must be aware of the legal ramifications associated with mishandling data. By fostering a culture of responsibility and accountability, agencies can safeguard their operations and maintain client trust. Regularly updating training and safety measures ensures investigators stay ahead of potential risks in a rapidly evolving digital landscape.
Identifying and Mitigating Data Breaches
Data breaches present significant risks in the realm of private investigations. Detecting potential vulnerabilities requires a systematic approach. Investigators should regularly evaluate data access protocols. Conducting audits on storage systems can reveal weaknesses. Employing intrusion detection systems aids in early identification of suspicious activities. Such measures allow for timely responses to potential breaches.
Mitigation strategies are essential once a breach is identified. Implementing robust encryption techniques can safeguard sensitive information from unauthorized access. Training staff on best practices in data security reinforces the importance of vigilance. Establishing a clear incident response plan ensures that investigators know how to act swiftly. These proactive steps can greatly reduce the impact of data breaches on investigative operations.
Training and Best Practices for Investigators
Ongoing training is essential for private investigators to stay abreast of the evolving landscape of data handling. Regular workshops and seminars can enhance their understanding of legal frameworks surrounding data privacy and the implications of improper practices. Practical sessions that focus on real-world scenarios encourage critical thinking and problem-solving skills. Investigators should also familiarise themselves with the latest technological advancements that aid in secure data management and retrieval.
Emphasising best practices in data handling can lead to improved operational efficiency. Documenting procedures for collecting, storing, and sharing information ensures consistency and accountability. Implementing a comprehensive data management policy not only reduces the risk of breaches but also enhances overall trustworthiness with clients. Private investigators should seek feedback on their methods and adapt wherever necessary to ensure they adhere to the highest standards in their field.
Continuous Education on Data Handling
Ongoing training is essential for private investigators, ensuring they remain well-versed in the evolving landscape of data handling. This education often encompasses workshops, seminars, and online courses covering the latest legislation, techniques, and technologies relevant to the field. Familiarity with current laws, including privacy regulations, is vital for maintaining compliance and safeguarding client information.
Additionally, participation in professional associations can provide valuable resources and networking opportunities for investigators. These connections facilitate the exchange of best practices and insights into emerging threats in data management. Investigators who prioritise continuous education not only enhance their skills but also bolster their credibility in the eyes of clients. This commitment to lifelong learning is crucial in a profession where data integrity and security are paramount.
FAQS
What are some common techniques for data retrieval used by private investigators in Sydney?
Common techniques for data retrieval include online searches, database access, social media analysis, and physical surveillance, among others.
What tools and technologies do private investigators use for data handling?
Private investigators often use advanced software for data analysis, GPS tracking devices, surveillance cameras, and digital forensics tools to manage and handle data effectively.
How can private investigators manage risks associated with data handling?
Risk management in data handling involves implementing strict data security protocols, regular audits, and adopting a risk assessment framework to identify potential vulnerabilities.
What steps should be taken to identify and mitigate data breaches?
Identifying data breaches includes monitoring data access logs, conducting regular security assessments, and implementing immediate response plans to contain breaches and mitigate further risks.
Why is continuous education important for private investigators regarding data handling?
Continuous education is crucial as it ensures private investigators stay updated on the latest data protection laws, technological advancements, and best practices in data handling to enhance their investigative effectiveness.
Related Links
Confidentiality Challenges in Digital InvestigationsProtecting Sensitive Information During Investigations
Maintaining Trust: How Confidentiality Affects Client Relationships
The Impact of the Privacy Act on Investigation Practices
Understanding Confidentiality Agreements in Investigative Work