Key Considerations for Compliance with the Australian Privacy Principles
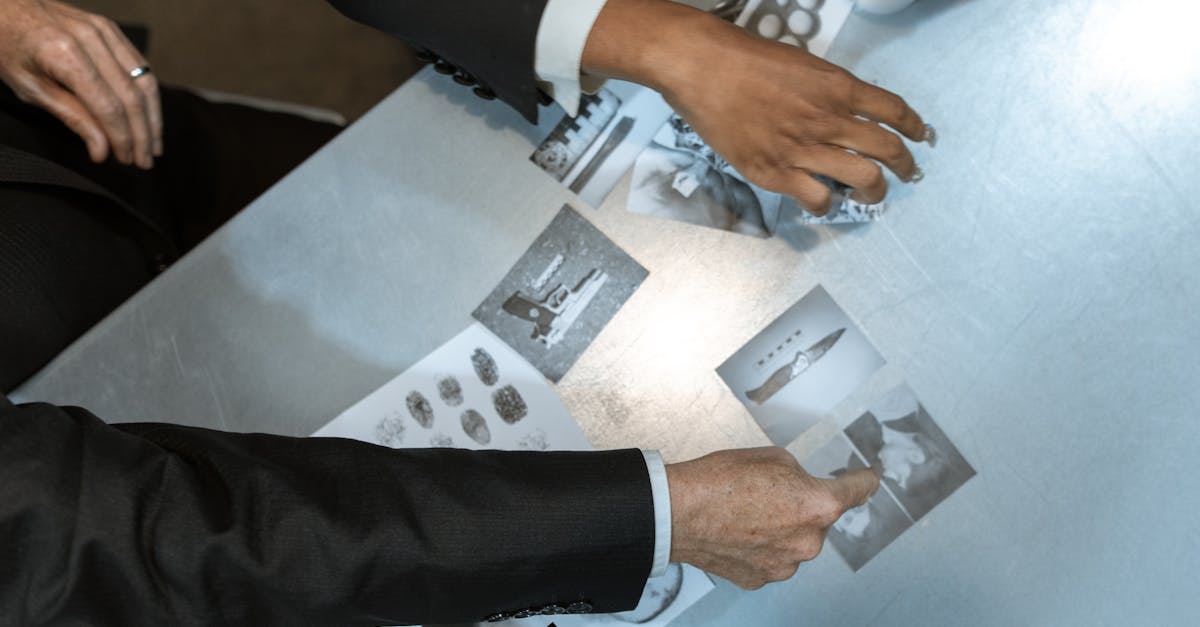
Table Of Contents
Data Security Measures
Organisations must prioritise robust data security measures to protect personal information and comply with the Australian Privacy Principles. Implementing strong access controls is essential for limiting who can view and handle sensitive data. Regular audits of security systems allow organisations to identify vulnerabilities and update their protective measures accordingly. Encryption should be a standard practice for data both in transit and at rest, ensuring that even if unauthorised access occurs, the information remains secure.
Training staff on data protection practices is crucial in fostering a culture of compliance within an organisation. Employees should be informed about potential security threats, such as phishing scams and social engineering tactics. Following best practices in data handling procedures minimises the risk of accidental exposure. Establishing an incident response plan will also prepare an organisation to address any security breaches swiftly and effectively.
Implementing Robust Security Protocols
Establishing strong security protocols is essential for protecting sensitive data in compliance with the Australian Privacy Principles. Organisations should conduct regular risk assessments to identify potential vulnerabilities in their systems. Implementing encryption for both data at rest and data in transit adds an additional layer of security. Regular software updates and patches help protect against known vulnerabilities. Additionally, employing multi-factor authentication can significantly reduce the risk of unauthorised access.
Training staff on best practices for data security is equally important. Employees must understand the significance of strong passwords and recognise phishing attempts to safeguard sensitive information. Moreover, creating a culture of privacy awareness ensures that all team members prioritise data protection in their daily activities. Regular audits of security measures can help identify areas for improvement and ensure compliance with relevant regulations.
Handling Data Breaches
Data breaches can occur despite the best security measures in place. When a breach happens, it is crucial to act swiftly and assess the situation. The first step is to identify the nature and extent of the breach. This includes determining which data has been compromised, the potential risks involved, and the parties affected. Documentation throughout this process is essential for understanding what occurred.
Once the breach has been assessed, notifying the affected individuals is a priority. Transparency is important in maintaining trust. Clear communication regarding the breach, including what information was exposed and what actions are being taken, should be provided. In addition, organisations must report the incident to the Office of the Australian Information Commissioner if it meets the threshold for notifiable data breaches. Following these steps helps ensure compliance with legal obligations while mitigating the impact of the breach.
Steps to Take Following a Breach
The immediate response to a data breach involves assessing the situation to determine the extent of compromised information. Identifying the affected individuals and the nature of the breach is crucial. This process enables organisations to inform all stakeholders effectively while ensuring compliance with legal obligations. Security teams must collaborate with legal advisors to evaluate potential risks and devise a communication strategy.
Once the initial assessment is complete, notifying affected parties becomes essential. Timely communication fosters transparency and helps individuals take necessary precautions against potential misuse of their data. Additionally, organisations should report the breach to the Office of the Australian Information Commissioner (OAIC) when required. Evaluating current security measures and implementing improvements will aid in preventing future incidents while reinforcing trust with customers.
Privacy Policies and Transparency
A well-crafted privacy policy serves as a fundamental component of an organisation’s compliance strategy. It must clearly outline the types of personal information collected, the purpose of collection, and how that information will be used and stored. Transparency is essential, ensuring that individuals understand their rights regarding their data. This includes informing them about any potential sharing with third parties and the measures taken to protect their information.
Maintaining an accessible privacy policy builds trust between the organisation and its stakeholders. Regular reviews and updates are necessary to reflect changes in data handling practices or legislative requirements. Providing clear and unambiguous language helps demystify the policies for consumers. This approach not only aligns with the Australian Privacy Principles but also encourages a culture of transparency and accountability within the organisation.
Crafting Clear and Compliant Privacy Notices
Creating effective privacy notices requires clarity and simplicity. Organisations should focus on using plain language that is easily understood by individuals. Technical jargon and legalese can create confusion. Including key information such as the types of data collected, the purposes for collection, and the rights of individuals is essential. Transparency helps individuals understand how their information will be used and can foster a sense of trust between consumers and organisations.
Incorporating the Australian Privacy Principles into these notices ensures compliance with legal requirements. Businesses should assess their specific practices and tailor privacy notifications accordingly. Regular updates to privacy notices may be necessary to reflect changes in data handling practices or legislation. It is important to provide contact details for individuals with questions or concerns about their privacy. This proactive approach can enhance accountability and encourage a positive relationship with data subjects.
FAQS
What are the Australian Privacy Principles (APPs)?
The Australian Privacy Principles are a set of guidelines established under the Privacy Act 1988 that govern how personal information is collected, used, disclosed, and stored by Australian government agencies and private organisations.
How can businesses ensure compliance with the APPs?
Businesses can ensure compliance by implementing robust data security measures, developing clear privacy policies, training staff on privacy obligations, and regularly reviewing their practices to align with the APPs.
What should a business do if it experiences a data breach?
If a data breach occurs, a business should immediately assess the situation, contain the breach, notify affected individuals if required, and report the breach to the Office of the Australian Information Commissioner (OAIC) if it's likely to result in serious harm.
What are the key elements of a compliant privacy notice?
A compliant privacy notice should include information on the types of personal data collected, the purposes for collection, how the data will be used and disclosed, how individuals can access their data, and the organisation's contact details for privacy inquiries.
Why is transparency important in handling personal data?
Transparency is crucial as it builds trust with customers, ensures compliance with legal obligations, and allows individuals to make informed decisions about their personal information, ultimately enhancing a business's reputation and customer loyalty.
Related Links
The Role of Consent in Private Investigations under Australian LawAn Overview of Privacy Laws Affecting Private Investigators in Australia
Challenges Faced by Private Investigators in Upholding Privacy Standards
Recent Amendments to Privacy Laws and Their Impact on Investigations
How the Right to Privacy Shapes Investigative Practices in Australia
The Importance of Ethical Conduct in Adhering to Privacy Laws